Today’s additive manufacturing market is a $5 billion worldwide business in which computer aided designs often traverse the internet, email, or cloud-based services from owner to often-remote three-dimensional (3D) printers. These risky transits and the widespread availability of 3D printers, constitute a vast opportunity for hackers and thieves prowling for back doors to print unauthorized parts from stolen intellectual property, or reverse engineer genuinely acquired parts to create counterfeits. Theft of intellectual property alone costs manufacturers billions of dollars a year.

Computer aided design of a cube with embedded QR code segmented into 320 small cubes in isomeric view (left-hand image). Three views normal to each other (three right-hand images). Only the first of these three images will give the correct reading orientation (large cube is 10 x 10 x 10 mm3 and 320 small cubes are 0.36 x 036 x 0.36 mm3 each).
So far, schemes to authenticate genuine products have relied on traditional methods such as stamping a serial number or tracking code on the parts’ surface, but they are easy to remove or duplicate. Researchers from the New York University have developed an intriguing alternative.
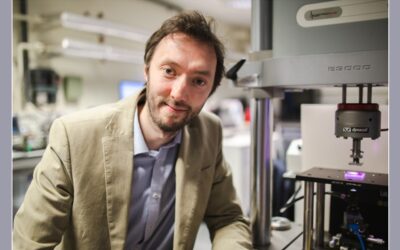
Led by Prof. Nikhil Gupta, a team of researchers from NYU Tandon School of Engineering and NYU Abu Dhabi converted quick response (QR) codes, bar codes, and other passive tags into 3D features hidden within the part in a way that they does not compromise the part’s integrity. This embedded code is scanned by a micro-computed tomography scanner for authentication purposes.
Their scheme explodes the code into hundreds of small parts to hide the actual code, even in plain sight. This way, it can only be read correctly from one orientation. From any other of potentially infinite orientations the code presents “false faces”—dummy QR tags. The embedded features do not weaken the structural integrity of the part because the entire code is spread over large number of 3D-printed layers.
First author Fei Chen commented; “This method allows manufacturers to protect their design, and the suppliers or customers now have a way to authenticate the parts.”
“We tested the scheme on thermoplastics, photopolymers, and metal alloys, with several printing technologies, and found it to work efficiently,” said Prof. Gupta, adding that “exploding the code into a large number of parts also makes it practically impossible to reverse engineer it.”
Kindly contributed by Karl P. Greenberg.